Vulnerability Management Process Flow Chart
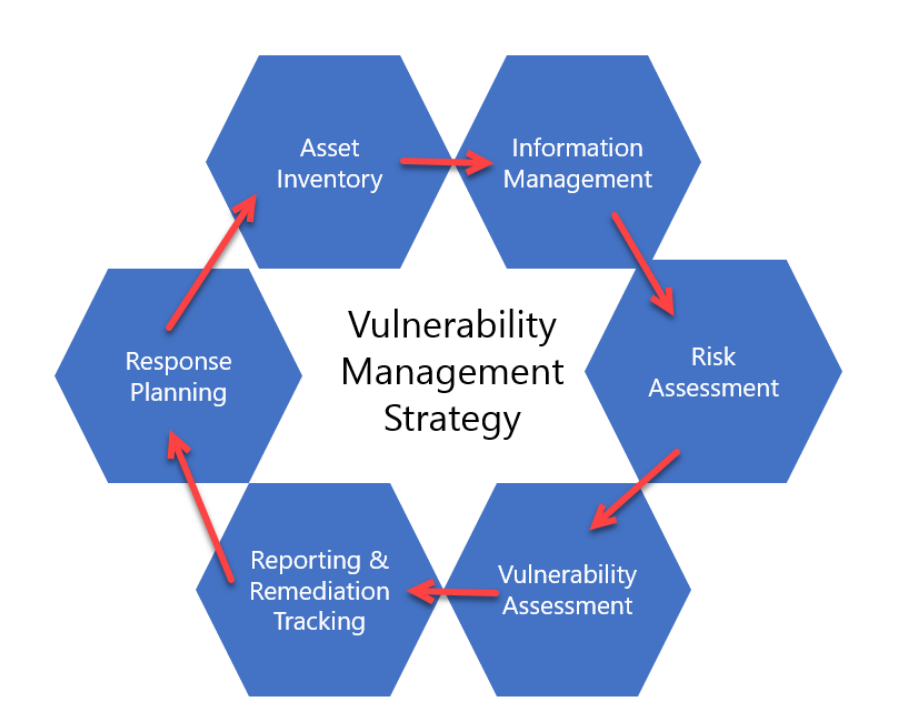
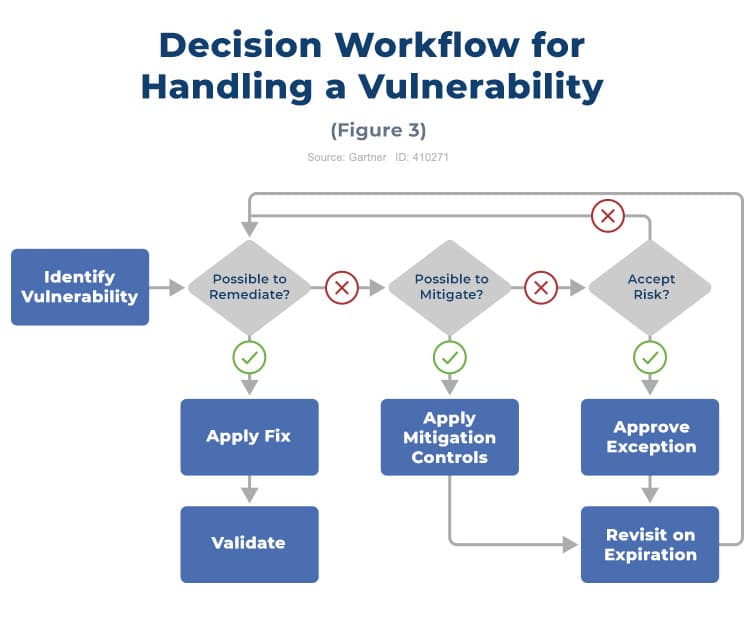
Vulnerability Management Process Flow Chart - Web a vulnerability management process diagram typically consists of several stages that help identify, prioritize, remediate, and verify vulnerabilities within an organization’s it infrastructure. Our templates provide a visual roadmap for your vulnerability management process, ensuring that complex concepts are communicated. Web learn the best practices for implementing a sustainable vulnerability management process, including establishing clear objectives, selecting appropriate tools, maintaining historical data, and acknowledging risks. There are five main stages in the vulnerability management cycle include: Web what are the 5 steps of the vulnerability management lifecycle. Finding vulnerabilities through scanning and testing, prioritising, fixing, and monitoring vulnerabilities. Web 4 steps of the vulnerability management process. Understand exposure of all of your assets including vulnerabilities, misconfigurations and other security health indicators. ★ “vulnerability management is the cyclical practice of identifying, classifying, remediating, and mitigating vulnerabilities”. Web our vulnerability management process flow chart powerpoint templates empower users to address vulnerabilities comprehensively. The goal of this study is to call attention to something that is often. Web this guide is intended for organizations seeking help in establishing a vulnerability management process. If you find conflicting information please raise it to the attention of the security team. Web our vulnerability management process flow chart powerpoint templates empower users to address vulnerabilities comprehensively. Vulnerability. ★vulnerability management is an integral part of computer and network security, and must not be confused with a vulnerability assessment. Understand exposure of all of your assets including vulnerabilities, misconfigurations and other security health indicators. The process areas described include • developing a vulnerability analysis and resolution strategy • developing a vulnerability management plan • developing a vulnerability discovery capability. Web the vulnerability remediation process is a workflow that fixes or neutralizes detected weaknesses including bugs and vulnerabilities. Web 4 steps of the vulnerability management process. Web the vulnerability management process is a continuous process for discovering, prioritizing, and resolving security vulnerabilities across an organization’s it infrastructure. Web in cybersecurity, vulnerability management is the process of identifying, analyzing, and managing. Web our vulnerability management process flow chart powerpoint templates empower users to address vulnerabilities comprehensively. Organizations can improve their overall security posture by implementing a systematic approach to managing vulnerabilities and configuration weaknesses across it assets. Web there are five stages in the vulnerability management process: Identify and map all of your assets across all of your computing environments. Web. The scan consists of four stages: Web 4 steps of the vulnerability management process. Finding vulnerabilities through scanning and testing, prioritising, fixing, and monitoring vulnerabilities. Web the guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification/scanning phase, the reporting phase, and remediation phase. Web a vulnerability management process diagram typically consists. The goal of this study is to call attention to something that is often. Web the guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification/scanning phase, the reporting phase, and remediation phase. Web learn the best practices for implementing a sustainable vulnerability management process, including establishing clear objectives, selecting appropriate tools,. How we set up our tools for vulnerability testing, how we group our assets for scans and reporting, how we prioritize remediation, what metrics we would use in our reports, what exceptions from remediation are acceptable and what are not. Web 4 steps of the vulnerability management process. Web what are the 5 steps of the vulnerability management lifecycle. Web. The process areas described include • developing a vulnerability analysis and resolution strategy • developing a vulnerability management plan • developing a vulnerability discovery capability Our templates provide a visual roadmap for your vulnerability management process, ensuring that complex concepts are communicated. Assessment is the first stage of the cycle. Web this paper looks at how a vulnerability management (vm). The process areas described include • developing a vulnerability analysis and resolution strategy • developing a vulnerability management plan • developing a vulnerability discovery capability Web there are five stages in the vulnerability management process: Our templates provide a visual roadmap for your vulnerability management process, ensuring that complex concepts are communicated. Web the vulnerability remediation process is a workflow. Understand exposure of all of your assets including vulnerabilities, misconfigurations and other security health indicators. Vulnerability management is essential to every modern cyber security strategy. Web our vulnerability management process flow chart powerpoint templates empower users to address vulnerabilities comprehensively. Web in cybersecurity, vulnerability management is the process of identifying, analyzing, and managing vulnerabilities within an operating environment in order. Create and refine policy and slas. Understand exposure of all of your assets including vulnerabilities, misconfigurations and other security health indicators. This document details how to execute the vulnerability management process as documented in our vulnerability management policy. ★vulnerability management is an integral part of computer and network security, and must not be confused with a vulnerability assessment. Assessment is the first stage of the cycle. Finding vulnerabilities through scanning and testing, prioritising, fixing, and monitoring vulnerabilities. Web for instance, 1.1 scope influences multiple processes: There are five main stages in the vulnerability management cycle include: Web 4 steps of the vulnerability management process. Follow these five main steps of the vulnerability management process to strengthen your cybersecurity. Web this paper looks at how a vulnerability management (vm) process could be designed and implemented within an organization. The scan consists of four stages: Web the guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification/scanning phase, the reporting phase, and remediation phase. This is the first stage in the vulnerability management process diagram. Hackers discover external attack surfaces cybercriminals can exploit. The goal of this study is to call attention to something that is often.
Vulnerability Management Process Flow Chart Rootshell
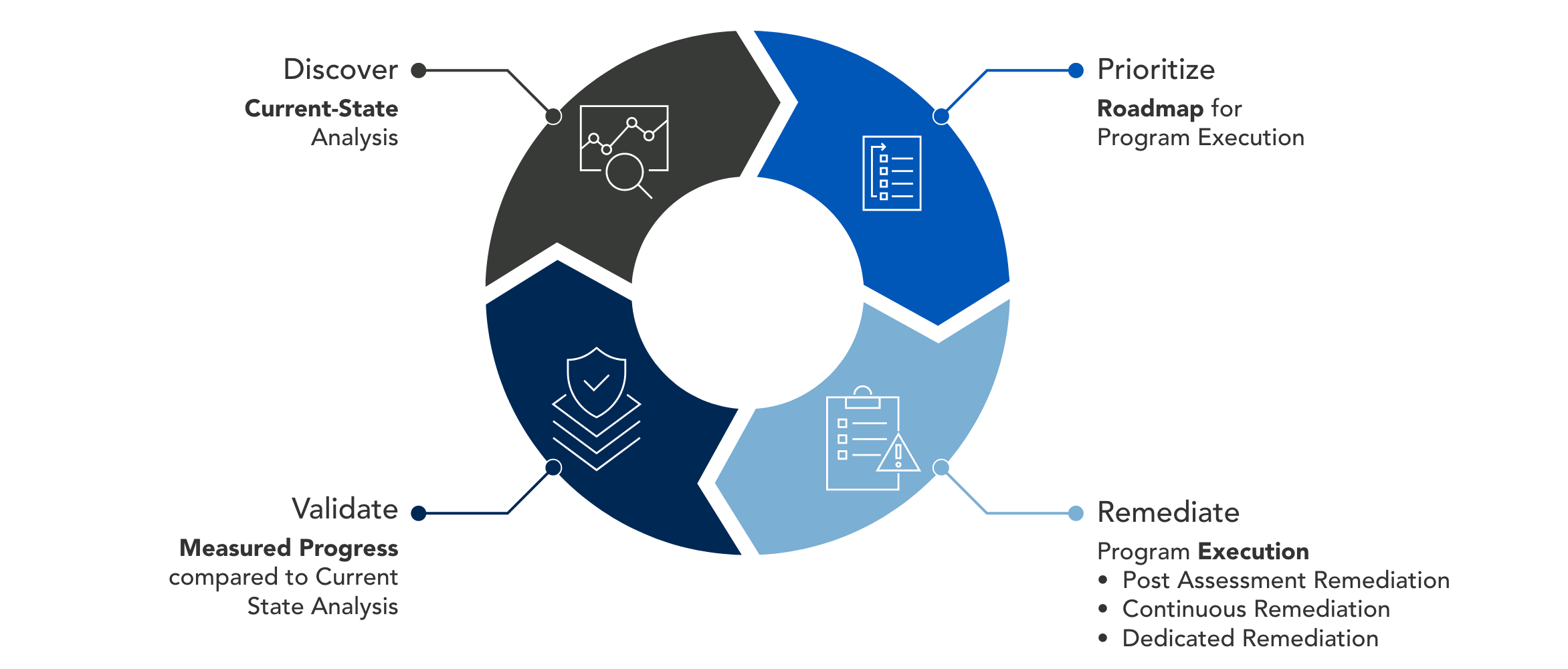
Vulnerability Management Services Optiv
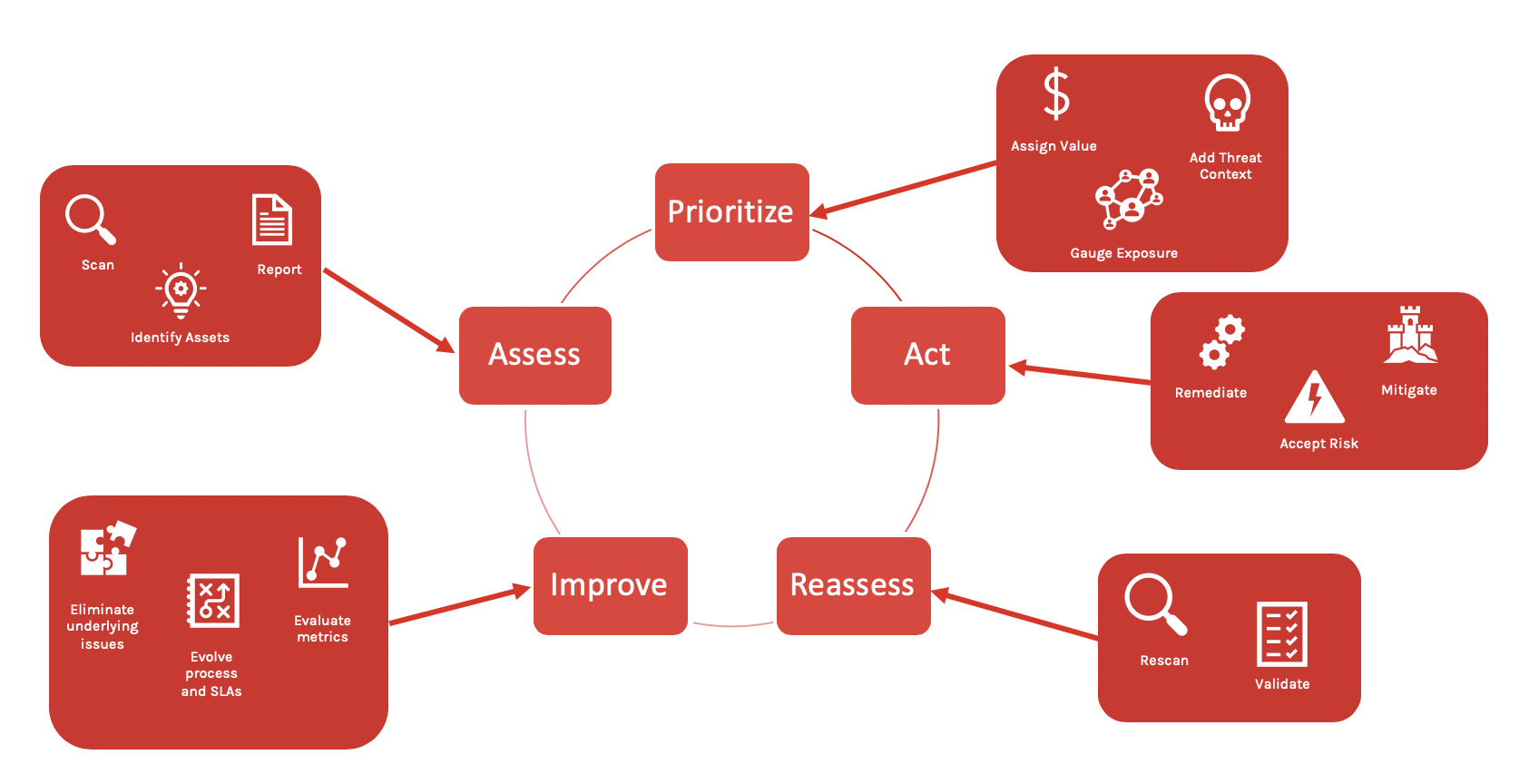
The Vulnerability Management Lifecycle (5 Steps) CrowdStrike
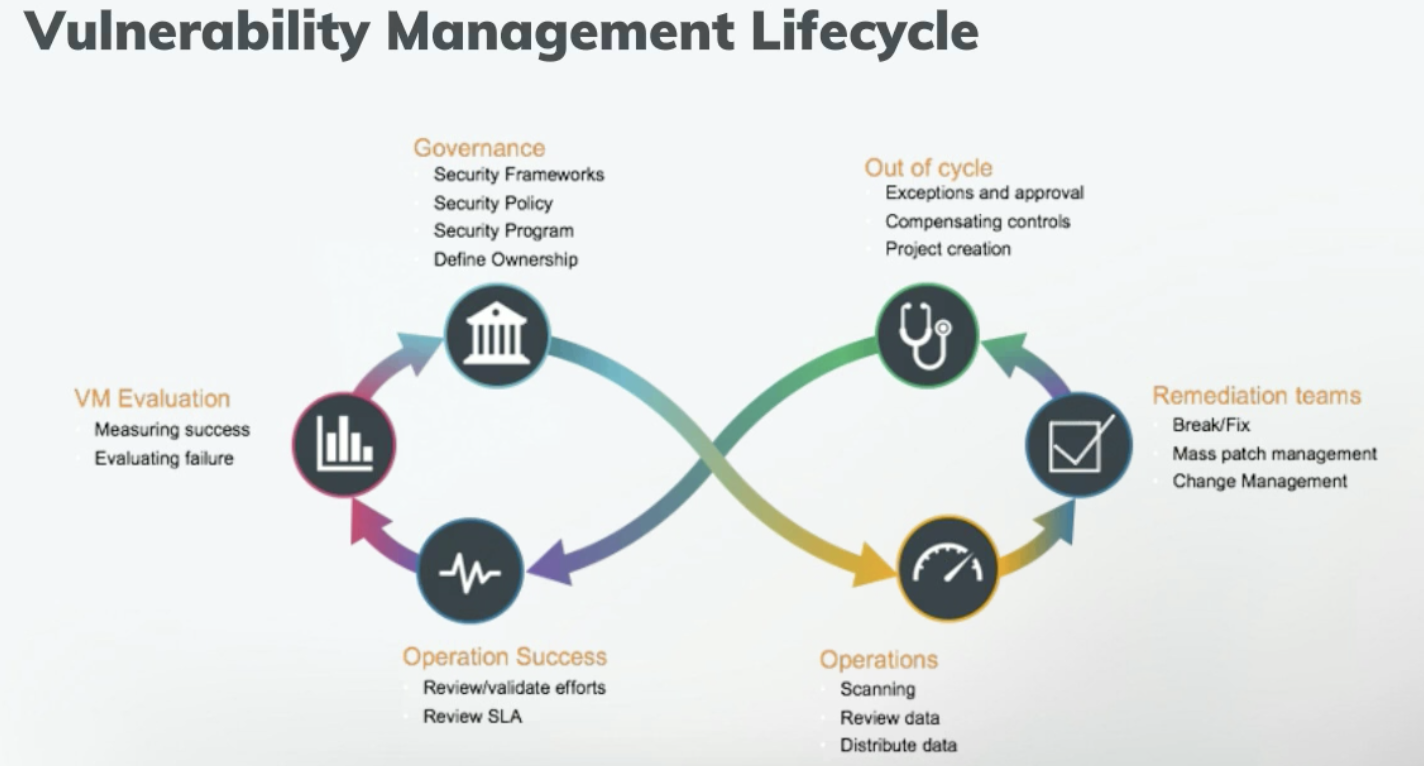
An effective vulnerability management lifecycle Entrepreneur Business
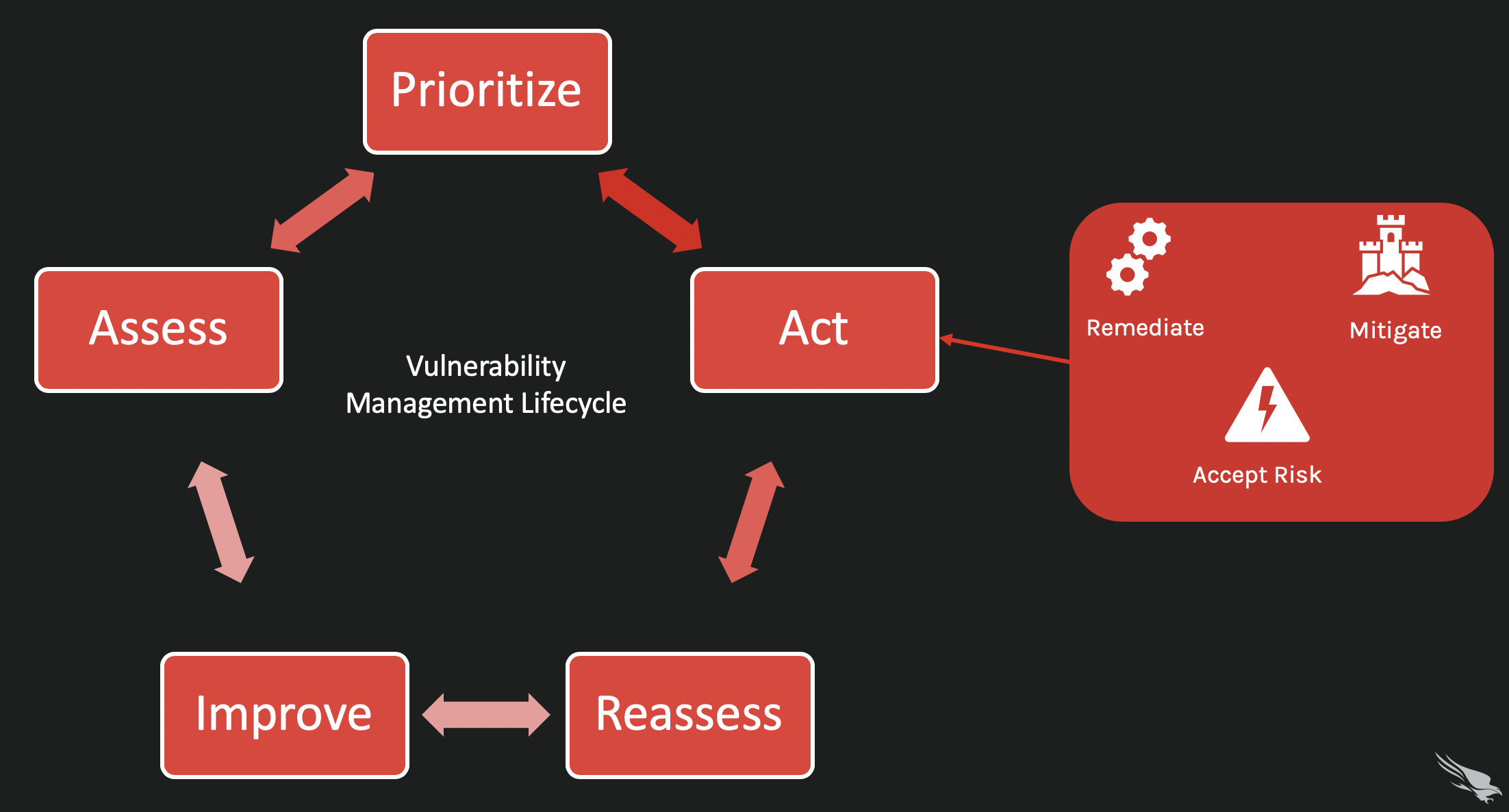
The Vulnerability Management Lifecycle (5 Steps) CrowdStrike
Vulnerability Management Process Flow Chart
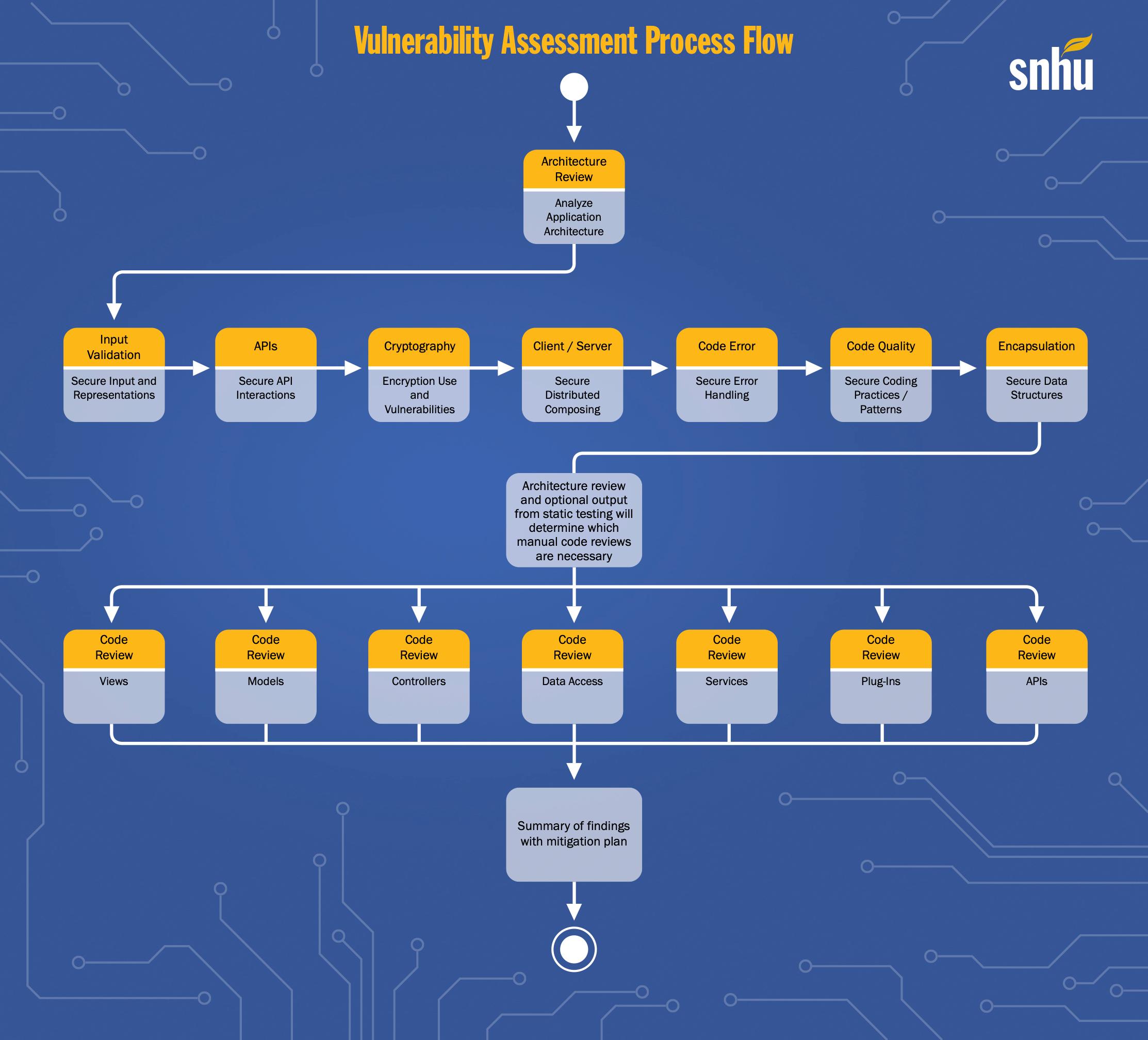
Using the Vulnerability Assessment Process Flow
Vulnerability Management Process Flow Chart Rootshell
Vulnerability Management Process Template
Vulnerability Management Process, what is it? Conviso AppSec
The Process Areas Described Include • Developing A Vulnerability Analysis And Resolution Strategy • Developing A Vulnerability Management Plan • Developing A Vulnerability Discovery Capability
Organizations Can Improve Their Overall Security Posture By Implementing A Systematic Approach To Managing Vulnerabilities And Configuration Weaknesses Across It Assets.
Vulnerability Management Is Essential To Every Modern Cyber Security Strategy.
Web This Guide Is Intended For Organizations Seeking Help In Establishing A Vulnerability Management Process.
Related Post: